VulnParse-Pin is a vulnerability intelligence and decision support engine for teams that need consistent, explainable risk prioritization from scanner output.
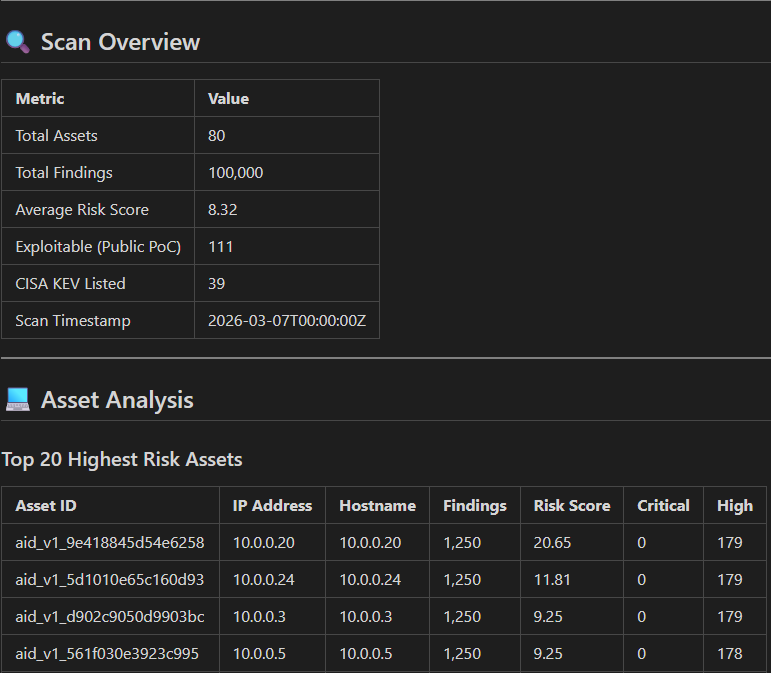
It ingests vulnerability reports (currently Nessus XML and OpenVAS XML), normalizes findings into a common model, enriches them with threat intelligence, computes risk scores, and ranks what to fix first.
What it is
- A CLI-first vulnerability parsing and prioritization platform
- A deterministic pipeline: parse → enrich → score → rank → export
- A transparent scoring system with configurable weighting and risk bands
- A high-volume capable engine optimized for large finding sets
What problem it solves
Security teams often face:
- Inconsistent scanner formats and schemas
- Manual triage bottlenecks and alert fatigue
- Fragmented enrichment from KEV, EPSS, NVD, and exploit sources
- Opaque risk calculations that are hard to audit or explain
VulnParse-Pin addresses this by standardizing data, centralizing enrichment, and producing reproducible risk outputs with clear provenance.
Philosophy and Principles
Context-Driven Prioritization: Prioritization is based on a comprehensive understanding of the vulnerability landscape, including exploitability, impact, and organizational relevance. This is determined by user-configurable policies that can be tuned to align with the organization's risk tolerance and priorities.
Explainability: VulnParse-Pin generates explainable artifacts that detail the factors contributing to each vulnerability's score and priority, enabling analysts to understand and trust the results.
Open Source: VulnParse-Pin is fully open source under the AGPLv3+ license, fostering transparency and community collaboration.
SSDLC Development: VulnParse-Pin is developed with security best practices in mind and focuses on Secure-By-Design principles first and foremost.
Extensibility: The architecture is designed to be modular and extensible, allowing for easy integration with existing tools and workflows, as well as customization to meet specific organizational needs.
Centralized Run-Context: All processing stages have access to a shared context that allows for dynamic decision-making and cross-pass communication, enabling more sophisticated prioritization logic.
Stable Contracts and APIs: VulnParse-Pin maintains stable input/output contracts and APIs to ensure that integrations and customizations remain functional across updates, fostering long-term adoption and community contributions.
Comprehensive Documentation: Clear and detailed documentation is provided to help users understand how to use, configure, and extend VulnParse-Pin effectively, as well as to encourage community contributions and collaboration.
Who it is for
- SOC analysts and vulnerability management teams
- Pentest and advisory organizations delivering client triage
- Security engineering teams building CI/CD security workflows
- Researchers and contributors needing auditable risk logic
Core capabilities
- Schema detection and parser selection for supported scanner formats
- Enrichment from KEV, EPSS, NVD, and Exploit-DB (online/offline modes)
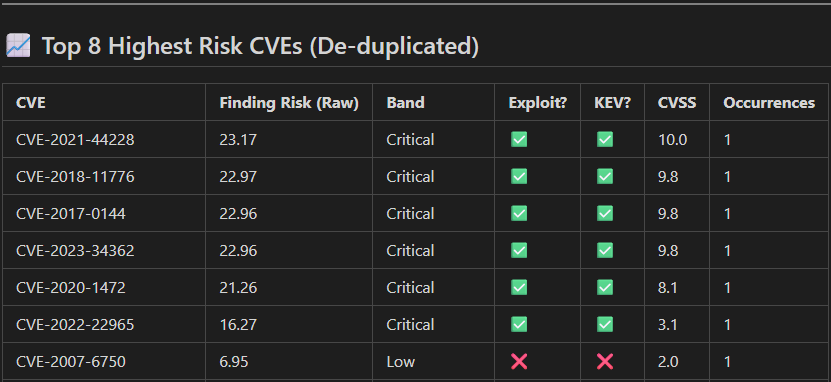
- Derived pass system for scoring and Top-N triage
- JSON and CSV export paths with secure defaults
- Presentation overlays for reporting consumers
Why organizations should use it
- Faster triage: converts raw findings into ranked remediation queues
- Better governance: explainable, configurable scoring policy
- Operational fit: scalable behavior from small scans to high-volume workloads
- Security posture: hardened I/O and sanitization controls in default flows
- Reduces MTTR: built-in enrichment and automated prioritization helps engineers focus more on patching and less on figuring out which ones matter more.